Which Cybersecurity Risks Are Most Dangerous to Small Businesses?
Small businesses face numerous cybersecurity threats that can jeopardize their operations, financial stability, and customer trust. Navigating these challenges requires a deep understanding of the risks and the implementation of effective defenses. This blog post will explore the most significant cybersecurity threats to small businesses and provide detailed strategies for mitigating these risks, helping you safeguard your business in a proactive manner.
1. Phishing and Social Engineering
What is Phishing?
Phishing attacks involve cybercriminals impersonating reputable entities to deceive individuals into providing sensitive information. This form of attack is particularly dangerous because it often serves as the precursor to more severe security breaches, exploiting human error rather than technical vulnerabilities.
Impact on Small Businesses
For small businesses, the consequences of phishing can be devastating, leading to significant financial losses and breaches of sensitive data. Such incidents can irreparably harm customer trust and tarnish a business’s reputation, which can be particularly damaging for smaller enterprises that rely heavily on their local and loyal customer base.
How to Combat Phishing Attacks
Protecting against phishing requires a multi-faceted approach. Firstly, implementing phishing-resistant multi-factor authentication (MFA) is essential, as it significantly reduces the risk of unauthorized access, even if credentials are compromised. Furthermore, advanced email security solutions can help filter out phishing attempts before they reach employees. Lastly, regular security awareness training that includes phishing simulations will equip employees with the necessary skills to recognize and appropriately respond to phishing attempts, thereby strengthening the human element of your cybersecurity defenses.
2. Ransomware and Malware
What is Ransomware?
Ransomware is a type of malicious software that encrypts a victim’s files, with the attacker then demanding a ransom to decrypt them. This threat is notorious for its ability to completely halt business operations by locking away essential data.
Ransomware's Impact on Small Businesses
Small businesses are particularly vulnerable to ransomware attacks due to their typically less robust cybersecurity defenses and the essential need for immediate access to digital resources. The interruption of services and potential loss of data can be crippling, and many small businesses are forced to pay the ransom, which further encourages cybercriminals.
Preventing Ransomware Attacks
To prevent ransomware, small businesses should invest in comprehensive cybersecurity measures such as secure endpoint protection and robust data backup systems. These measures ensure that even if data is encrypted, the business can restore its information from backups without paying the ransom. Additionally, adopting a zero-trust security framework, which involves continuously verifying the legitimacy of all users and devices, can significantly enhance an organization's resilience against ransomware.
3. Weak Passwords
The Danger of Weak Passwords
Weak passwords represent a significant security risk as they are easily breached, allowing attackers straightforward access to sensitive systems and information. This is especially problematic in a small business setting where a single breach can give attackers access to the entirety of the business’s digital assets.
Strategies for Enhancing Password Security
Improving password security involves several strategies. Enforcing strong, unique passwords through stringent password policies and the use of password managers can help secure an organization's credentials. Transitioning to passwordless authentication methods, such as biometric scans or hardware tokens, reduces dependence on traditional passwords and enhances security by utilizing factors that are much harder for attackers to replicate.
4. Poor Patch Management
Risks of Inadequate Software Updates
Neglecting software updates exposes businesses to known vulnerabilities that cybercriminals can exploit to gain unauthorized access or deploy malware. These vulnerabilities are particularly dangerous because they are often well-documented and publicly known, making them easy targets for attackers.
Best Practices for Patch Management
Implementing an automated patch management system is essential for ensuring that all software is up-to-date and secure. This system can automatically apply updates and patches to software, closing off vulnerabilities before attackers can exploit them. Additionally, regularly conducting audits and updates is essential to maintain security across all devices and software, which can be particularly challenging in resource-limited environments.
Strategies for Cybersecurity Risks
Cybersecurity is an essential consideration for small businesses aiming to protect their operations and reputation. By understanding and mitigating the risks of phishing, ransomware, weak passwords, and poor patch management, businesses can significantly improve their security posture and resilience against cybersecurity risks.
Don't let your business be vulnerable to cyber threats. Partner with Unique Computing Solutions to enhance your cybersecurity measures. Our expert team offers tailored solutions to protect small businesses from sophisticated digital threats. Visit Unique Computing Solutions today to discover how we can help secure your business against evolving cybersecurity risks. Equip your business with the tools it needs to thrive safely in the digital era.
Transforming Customer Service: The Critical Role of IT Support
In the modern marketplace, stellar customer service is not just expected; it’s essential. Businesses compete not only on product quality but also on delivering exceptional customer experiences. In this digital age, Information Technology (IT) support has emerged as a cornerstone of this new paradigm. It goes beyond fixing technical issues; it plays a pivotal role in ensuring that customers enjoy seamless, uninterrupted services. By addressing technical challenges swiftly and efficiently, IT teams directly contribute to a positive, satisfying customer experience. This integration of technology and customer service is transforming businesses, propelling them towards greater customer satisfaction and loyalty.
The Evolution of IT Support
IT support has evolved dramatically from its humble beginnings. Initially, it was all about fixing broken machines and troubleshooting hardware problems. As technology advanced, so did the scope of IT support, expanding into software, networks, and now cloud services. Today, IT is not just a back-office function; it has become integral to customer service. Businesses rely on IT support to ensure their services are always available, secure, and functioning at peak performance. This evolution reflects the changing landscape of business operations, where digital presence and online services are now central to customer satisfaction and business success.
Understanding Customer Needs
Identifying and understanding customer needs is crucial for providing exceptional service. Each customer has unique expectations, whether it’s speed, reliability, accessibility, or security. IT support plays a critical role in meeting these expectations by resolving technical issues quickly and effectively. By doing so, IT support ensures that customers have a smooth and positive experience with your services, leading to increased satisfaction and loyalty. In this digital age, understanding and promptly addressing these needs through efficient IT support can set a business apart from its competitors.
Enhancing Communication with IT Support
Effective communication channels are vital in modern customer service. IT support can greatly enhance this communication by providing multiple platforms (such as chat, email, and phone support) that cater to different customer preferences. This variety ensures that customers can easily reach out for help in ways that are most convenient for them. Furthermore, IT support can use these channels to proactively communicate with customers about potential issues, updates, and solutions, thus improving overall customer experience and satisfaction.
IT Support and Customer Satisfaction
Efficient IT support directly correlates with higher customer satisfaction. Studies have shown that rapid response and resolution times lead to positive customer reviews and increased loyalty. Furthermore, IT support can personalize customer experiences through technology by using data analytics to understand preferences and predict needs, thereby offering solutions even before problems arise. This proactive approach not only resolves issues quickly but also demonstrates a commitment to customer care, significantly enhancing satisfaction.
Reducing Downtime with Proactive IT Support
Reducing downtime is crucial for enhancing customer experience, as it ensures continuous access to services and minimizes frustration. Proactive IT support plays a key role in this by monitoring systems for potential issues and addressing them before they impact customers. This approach not only maintains service reliability but also builds trust and satisfaction among users.
The Future of IT in Customer Service
The future of IT support in customer service is likely to be shaped by emerging technologies like artificial intelligence, machine learning, and automation. These advancements are expected to streamline the resolution process, reduce response times, and offer more personalized experiences. Predictions also suggest a shift towards more predictive IT support, where potential issues are identified and resolved before they can impact the customer, further enhancing the overall customer service experience.
Integrating IT into Your Business Strategy
To integrate IT support effectively into your business strategy, consider aligning IT objectives with customer service goals to ensure a unified approach. Regular training and development for staff are crucial to keep them updated on the latest technologies and customer service techniques. This ensures they can provide the best possible support and contribute positively to the overall customer experience.
Unique Computing Solutions: Your Partner in Enhancing Customer Experience
Unique Computing Solutions offers specialized IT services that can significantly improve your customer service by ensuring your technology operates seamlessly. Their services actively cater to your business's unique needs, enhancing IT infrastructure and customer interaction.
Empowering Your Customer Service with IT Support
Effective IT support is crucial for delivering outstanding customer service. By understanding customer needs, enhancing communication, and reducing downtime, it plays a vital role in business success.
Consider the current state of your IT support and how it impacts your customer service. Contact Unique Computing Solutions for a personalized strategy that aligns with your business needs and customer service goals.
IT Support Services: Shielding Businesses Against Cyber Threats
In today's interconnected digital landscape, businesses rely heavily on technology to drive operations, connect with customers, and stay competitive. However, with increased reliance on digital platforms comes the heightened risk of cyber threats, data breaches, and system vulnerabilities. To navigate these challenges effectively, businesses must prioritize robust IT support services that can provide comprehensive solutions tailored to their needs.
Understanding Cybersecurity Challenges
Cybersecurity stands as one of the most pressing concerns for businesses in the digital age. The evolving nature of cyber threats, ranging from malware and phishing attacks to ransomware and insider threats, poses significant risks to the integrity and security of business data. A breach in cybersecurity can lead to financial losses, damage to reputation, and legal implications for businesses.
Moreover, the proliferation of remote work and mobile devices has expanded the attack surface for cybercriminals, making it even more challenging for businesses to defend against threats effectively. As businesses increasingly rely on cloud-based services and IoT devices, the complexity of cybersecurity threats continues to grow.
The Role of IT Support Services in Cybersecurity
Effective cybersecurity requires a proactive approach that goes beyond merely reacting to threats as they arise. This is where IT support services play a crucial role. IT support teams are equipped with the expertise and tools necessary to identify, mitigate, and prevent cyber threats before they can inflict harm on businesses.
IT support services monitor networks and systems, enabling real-time detection and response to security incidents. Through threat intelligence gathering and analysis, IT support teams can stay ahead of emerging threats and adapt security measures accordingly.
In addition to proactive threat detection and response, IT support services help businesses implement robust security measures such as firewalls, antivirus software, and intrusion detection systems. These tools create layers of defense to safeguard business networks and data against cyber threats.
Regular security updates and patches are essential components of cybersecurity maintenance. IT support services ensure that businesses stay up-to-date with the latest security protocols and software updates, reducing the risk of vulnerabilities being exploited by cybercriminals.
Managing Data Effectively
In the digital era, data has emerged as one of the most valuable assets for businesses. However, managing vast volumes of data presents its own set of challenges, including storage limitations, data organization, and security concerns. Data breaches and unauthorized access to sensitive information can have devastating consequences for businesses, including financial losses, regulatory penalties, and damage to reputation.
IT support services play a vital role in helping businesses manage their data effectively and securely. By implementing data management solutions such as cloud storage and backup systems, IT support teams enable businesses to store and access data securely while minimizing the risk of data loss or corruption. Encryption techniques and access controls further enhance data security, ensuring that sensitive information remains protected from unauthorized access or interception.
Moreover, data management extends beyond security considerations to encompass data organization and accessibility. IT support services help businesses implement data governance policies and procedures to ensure compliance with regulatory requirements and industry standards. By establishing clear guidelines for data usage, storage, and sharing, businesses can minimize the risk of data breaches and maintain data integrity and confidentiality.
Leveraging IT Support Services for System Integration
In today's digital landscape, businesses depend on numerous software applications and systems for operations. However, integrating disparate systems and ensuring seamless communication between them can be a complex and challenging task. Compatibility issues, data synchronization errors, and technical constraints often hinder the effectiveness of system integration efforts, leading to inefficiencies and operational bottlenecks.
IT support services play a critical role in facilitating smooth and efficient system integration for businesses. With their expertise in software and hardware configurations, IT support teams can identify and address compatibility issues, streamline data flows, and optimize system performance. By leveraging advanced integration techniques and technologies, IT support services enable businesses to harness the full potential of their digital infrastructure, driving productivity and innovation.
Case Studies: Examples
To illustrate the transformative impact of IT support services on businesses, let's consider a few real-life examples:
Case Study 1: Retail Company X
Retail Company X faced frequent cybersecurity breaches, endangering customer trust and business reputation. By partnering with IT support services provider Unique Computing Solutions, Retail Company X was able to implement robust cybersecurity measures, including firewall protection, threat monitoring, and employee training programs. As a result, Retail Company X saw a significant reduction in cybersecurity incidents and improved customer confidence in their brand.
Case Study 2: Manufacturing Firm Y
Manufacturing Firm Y encountered system integration challenges due to legacy systems, affecting operational efficiency and data visibility. With the expertise of IT support services from Unique Computing Solutions, Manufacturing Firm Y underwent a comprehensive system integration overhaul, consolidating its disparate systems into a unified platform. This streamlined data flows, improved collaboration between departments, and enhanced overall productivity for Manufacturing Firm Y.
The Value of Partnering with Unique Computing Solutions
At UCS, we value the role of IT support services in safeguarding businesses, managing data, and optimizing system integration. With our experienced IT professionals and personalized approach, we deliver tailored IT support solutions to meet every business's unique needs.
By partnering with Unique Computing Solutions, businesses can:
- Benefit from proactive cybersecurity measures that protect against evolving cyber threats.
- Ensure the effective management and security of their valuable data assets.
- Drive operational efficiency and innovation through seamless system integration and optimization.
Safeguarding Your Business with Proactive IT Support Services
Ready to enhance your business's cybersecurity, data management, and system integration capabilities? Contact Unique Computing Solutions today for tailored IT support services that meet your specific needs and objectives. Visit our website or contact us to learn how we can protect your business from cyber threats.
Customer-Centric Tech: Innovations Transforming Satisfaction
In today's competitive business landscape, customer satisfaction stands as the cornerstone of success. As businesses increasingly prioritize customer-centricity, technology emerges as a powerful ally in enhancing these experiences. Welcome to the realm of customer-centric tech, where innovation converges with customer delight, redefining the way businesses engage with their audience.
At its core, customer-centric tech revolves around placing the customer at the forefront of every interaction and strategic decision. Leveraging advanced technological solutions, businesses aim to anticipate and fulfill the evolving needs and preferences of their customers. Customer-centric tech includes personalized recommendations and seamless omnichannel experiences to enhance overall customer satisfaction.
Understanding Customer-Centric Tech
Customer-centric tech revolves around the philosophy of prioritizing the customer's needs, preferences, and satisfaction in all aspects of business operations. Unlike traditional approaches that focus solely on products or services, customer-centric tech emphasizes building relationships and delivering personalized experiences. Key characteristics of customer-centric tech include adaptability, responsiveness, and a deep understanding of customer behaviors and preferences.
- Personalization Algorithms: Personalization algorithms analyze vast amounts of customer data to deliver tailored experiences. By leveraging data points such as past purchases, browsing history, and demographic information, businesses can customize product recommendations, marketing messages, and website content to resonate with individual customers. This level of personalization enhances engagement, fosters customer loyalty, and ultimately drives sales.
- Chatbots and Virtual Assistants: Chatbots and virtual assistants provide instant support and guidance to customers across various touchpoints. These AI tools handle queries, resolve issues, and complete transactions in real-time for seamless customer service. By automating routine tasks and providing round-the-clock assistance, chatbots and virtual assistants enhance accessibility and convenience for customers while freeing up human agents to focus on more complex inquiries.
- Self-Service Portals and Apps: Self-service portals and apps empower customers to access information, manage accounts, and resolve issues independently. Through intuitive interfaces and comprehensive self-help resources, these platforms offer a convenient alternative to traditional customer support channels. By enabling customers to find answers and complete tasks on their terms, self-service portals and apps improve efficiency, reduce wait times, and enhance overall satisfaction.
- Data Analytics for Customer Insights: Data analytics tools enable businesses to gain valuable insights into customer behaviors, preferences, and trends. By analyzing data from various sources such as transactions, social media interactions, and website visits, businesses can identify patterns, anticipate needs, and personalize experiences effectively. Data-driven insights inform strategic decision-making, enabling businesses to optimize products, services, and marketing campaigns to better meet customer expectations.
Transforming Satisfaction: How Customer-Centric Tech Enhances Experience
Personalization: Tailoring Experiences to Individual Preferences
Personalization is at the heart of customer-centric tech, allowing businesses to tailor experiences to individual preferences. Through dynamic content recommendations, algorithms analyze user behavior and preferences, dynamically suggesting content that is most relevant to each individual. Whether it's product suggestions, articles, or entertainment, these recommendations enhance engagement by presenting timely and personalized content, increasing the likelihood of conversion and fostering a stronger connection between the customer and the brand. Similarly, targeted marketing campaigns leverage data insights to create personalized messages that resonate with specific customer segments. By delivering tailored messages through various channels such as email, social media, and online advertisements, businesses capture the attention of their audience and drive conversion rates, demonstrating an understanding of customer's needs and preferences while strengthening brand loyalty.
Convenience: Empowering Customers with Self-Service Options
Customer-centric tech empowers customers with convenient self-service options, streamlining processes and transactions. Automation streamlines online purchases, account management, and support inquiries, without human intervention. This automation not only enhances convenience for customers but also reduces operational costs for businesses. Additionally, self-service options such as FAQ sections and knowledge bases provide customers with access to relevant information and resources to resolve common issues independently. By curating comprehensive libraries of frequently asked questions, troubleshooting guides, and tutorials, businesses empower customers to find answers to their queries at their own pace, reducing the burden on customer support teams and fostering a sense of autonomy among customers.
Seamless Integration: Creating Omnichannel Experiences
Creating seamless omnichannel experiences is essential for delivering consistent and cohesive interactions across multiple touchpoints. Customer-centric tech enables businesses to unify communication channels, allowing customers to interact seamlessly regardless of the channel used. Integrated communication systems ensure that customer inquiries are captured and addressed efficiently, enhancing accessibility and responsiveness. Furthermore, maintaining consistent branding and messaging across platforms is critical for building trust and reinforcing brand identity. Customer-centric tech facilitates the alignment of branding and messaging strategies across various platforms, ensuring a unified and coherent customer journey. By delivering consistent experiences across all channels, businesses enhance satisfaction and loyalty among customers, driving long-term success.
Examples of Customer-Centric Tech Success
Company A: Utilizing AI for Personalized Recommendations
Company A, a leading e-commerce retailer, has successfully leveraged AI technology to deliver personalized recommendations to its customers. The AI algorithms analyze vast customer data, generating tailored product recommendations. Through dynamic content displays and personalized email campaigns, customers are presented with products that align with their interests and preferences, enhancing their shopping experience and driving conversion rates. It has significantly boosted customer engagement and sales revenue, cementing its e-commerce leadership.
Company B: Implementing Self-Service Options for Improved Efficiency
Company B, a multinational telecommunications provider, has implemented self-service options to enhance customer satisfaction and operational efficiency. By introducing an intuitive online portal and mobile app, customers can now manage their accounts, troubleshoot technical issues, and make payments without the need for assistance from customer support representatives. This shift towards self-service has not only reduced the strain on Company B's customer support team but has also improved overall customer satisfaction by providing a convenient and accessible way for customers to address their needs. Through proactive communication and user-friendly interfaces, Company B has successfully transformed its customer service model, leading to higher customer retention rates and increased cost savings.
Company C: Creating a Seamless Omnichannel Experience for Customers
Company C, a leading retail chain, has prioritized creating a seamless omnichannel experience for its customers. By integrating its online and offline channels, Company C ensures a consistent and cohesive shopping experience across all touchpoints. Customers browse online, buy in-store, and access support across multiple channels. Through unified inventory management and order fulfillment systems, Company C provides customers with real-time visibility into product availability and delivery options, enhancing convenience and transparency. As a result, Company C has strengthened customer loyalty and increased sales by offering a seamless and integrated shopping experience that meets the evolving needs of today's consumers.
These case studies demonstrate how companies across different industries have successfully implemented customer-centric tech solutions to drive business growth and enhance customer satisfaction. By leveraging AI for personalized recommendations, implementing self-service options, and creating seamless omnichannel experiences, these companies have positioned themselves as leaders in delivering exceptional customer experiences.
Challenges and Considerations in Implementing Customer-Centric Tech
Data Privacy and Security Concerns
One of the foremost challenges in implementing customer-centric tech solutions revolves around data privacy and security concerns. Collecting and analyzing vast amounts of customer data inherently raises questions about how that data is stored, used, and protected. Businesses must navigate stringent regulations and compliance standards to ensure that customer information is safeguarded against unauthorized access, breaches, and misuse. Maintaining transparency and gaining customer trust in data practices is essential for long-term relationships.
Integration Complexity Across Systems
Integrating customer-centric tech solutions across disparate systems and platforms presents another significant challenge for businesses. Oftentimes, organizations operate with legacy systems that lack interoperability, making seamless integration a complex and time-consuming process. Siloed data and disjointed workflows hinder the ability to provide consistent and unified experiences across all touchpoints. Overcoming integration challenges demands careful planning, technology investment, and cross-department collaboration for smooth implementation aligning with business goals.
Balancing Automation with Human Touch
Balancing automation and human touch is critical in customer-centric tech implementation. While automation offers efficiency and scalability, there is a risk of alienating customers and eroding trust if interactions feel impersonal or devoid of empathy. Businesses must identify opportunities where automation can enhance processes and streamline workflows without sacrificing the human element of customer service. Empowering human agents with the tools and resources to personalize interactions, empathize with customers, and address complex inquiries is essential for maintaining a human-centric approach while leveraging technology to deliver exceptional experiences.
Addressing challenges requires a holistic approach, prioritizing ethical data use, seamless tech integration, and a customer-centric mindset valuing efficiency and empathy. By addressing challenges and refining strategies, businesses can implement customer-centric tech solutions driving value for both customers and the organization.
The Importance of Customer-Centric Tech
In exploring customer-centric tech, it's clear prioritizing the customer experience is crucial for business success in today's competitive landscape. By prioritizing the customer in every interaction and decision, businesses foster loyalty and drive growth. Customer-centric tech anticipates and meets evolving customer needs, delivering personalized, convenient, seamless experiences.
At Unique Computing Solutions, we understand the pivotal role that customer experience plays in driving business success. As tech and customer expectations evolve, prioritize customer-centricity in your strategy.
Empower your business with our innovative solutions tailored to enhance customer satisfaction, streamline operations, and drive growth. Whether personalized AI, seamless system integration, or IoT for customer service, we're here to guide you.
Can Network Management Boost Productivity?
In today's dynamic digital landscape, network efficiency and reliability are key to success. Moreover, at Unique Computing Solutions, we recognize the critical significance of effective network management in driving productivity and enabling businesses to thrive. Join us for an exploration of robust network management's impact on productivity, as we delve into its multifaceted benefits.
Understanding Network Management
Network management optimizes performance, security, and reliability. At Unique Computing Solutions, we specialize in providing tailored network support services designed to meet the diverse needs of our clients. From monitoring network traffic and ensuring data security to troubleshooting technical issues and optimizing network resources, effective network management is essential for maintaining a seamless and efficient operation that empowers businesses to achieve their objectives.
Enhanced Connectivity and Collaboration
Seamless Communication:
In today's interconnected business environment, seamless communication is fundamental for fostering collaboration and driving productivity. Efficient network management serves as the backbone for establishing reliable communication channels within organizations. Whether it's facilitating email correspondence, enabling instant messaging platforms, supporting video conferencing solutions, or integrating cloud-based collaboration tools, a well-managed network lays the foundation for smooth communication channels, fostering teamwork and productivity across all levels of the organization.
Remote Work Enablement:
The proliferation of remote work has heightened the importance of robust network management solutions. With an increasing number of employees opting for flexible work arrangements, businesses must ensure that their networks can support remote access securely and efficiently. Through strategic network management initiatives such as implementing virtual private networks (VPNs), optimizing bandwidth allocation, and strengthening cybersecurity measures, organizations can empower their remote workforce to remain productive and connected, irrespective of their physical location or device preferences.
Minimized Downtime and Disruptions
Proactive Monitoring and Maintenance:
One of the primary objectives of effective network management is to minimize downtime and disruptions. By implementing proactive monitoring and maintenance protocols, potential issues can be identified and addressed before they escalate into major problems. This proactive approach not only mitigates the risk of unexpected outages but also enhances overall system reliability, allowing employees to carry out their tasks without interruption.
Rapid Issue Resolution:
In the event of network issues, swift resolution is crucial to minimizing productivity loss. At Unique Computing Solutions, our expert team promptly resolves any network issues. Leveraging advanced troubleshooting techniques and drawing upon our extensive experience, we ensure that any downtime is kept to a minimum, enabling businesses to maintain optimal productivity levels and meet their operational objectives seamlessly.
Scalability and Flexibility
Accommodating Growth and Expansion:
As businesses evolve and expand, their network requirements evolve as well. Effective network management involves ensuring that the network infrastructure is scalable and flexible enough to accommodate growth and expansion seamlessly. Whether it involves onboarding new users, integrating emerging technologies, or expanding to new geographical locations, a well-managed network can adapt dynamically to meet the evolving needs of the business without sacrificing productivity or performance.
Agility in Adapting to Change:
In today's dynamic business landscape, agility is essential for staying competitive. A well-managed network enables organizational agility, adapting swiftly to market changes and technological advancements. By leveraging the latest network management tools and techniques, organizations can maintain a competitive edge while maximizing productivity and efficiency, positioning themselves for sustained success in a dynamic and unpredictable environment.
Enhanced Security and Compliance
Data Protection and Compliance:
In addition to productivity benefits, effective network management also plays a crucial role in ensuring data security and compliance. With rising cyber threats, businesses need robust security to protect sensitive data and meet regulations. From implementing firewalls and encryption protocols to conducting regular security audits and vulnerability assessments, a well-managed network helps mitigate security risks, protecting the integrity and confidentiality of the organization's data.
Regulatory Compliance:
Many industries are subject to strict regulatory requirements governing the protection and management of sensitive data. Effective network management ensures that businesses remain compliant with relevant regulations such as the General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), and Payment Card Industry Data Security Standard (PCI DSS). Adhering to regulatory standards helps organizations avoid fines, and reputational damage, and maintain trust with customers and stakeholders.
Empower Your Business with Effective Network Management
Effective network management is crucial for productivity, collaboration, and network support. Additionally, it ensures seamless operations and enhances communication within the organization. A well-managed network is crucial for competitive advantage, enabling seamless communication, minimizing disruptions, and ensuring security in today's digital landscape. At Unique Computing Solutions, we understand the critical role of reliable network support in achieving business objectives. If you're looking to optimize your network infrastructure and maximize productivity, we invite you to contact us today. Partner with us to tailor network solutions and drive your organization's success.
Contact Unique Computing Solutions today to explore our comprehensive network management services and boost productivity for your organization. Furthermore, our team is ready to provide tailored solutions to meet your specific needs and propel your business toward success
How Can Managed IT Services Benefit Small Businesses?
In today's fast-paced digital landscape, small businesses face numerous challenges when it comes to managing their IT infrastructure efficiently and cost-effectively. The evolving technology landscape, cybersecurity threats, and the need for scalability can be overwhelming for small business owners. This comprehensive guide explores in detail the numerous ways Managed IT Services can benefit small businesses, providing a deep understanding of this essential resource.
What Are Managed IT Services?
Before delving into the benefits, let's thoroughly understand what Managed IT Services entail. Managed IT Services involve outsourcing the management and maintenance of a business's IT infrastructure to a specialized provider. This provider, often referred to as a Managed Service Provider (MSP), takes care of various IT functions, including network management, cybersecurity, data backup, software updates, and more.
Benefits of Managed IT Services for Small Businesses
Cost Savings:
Small businesses often have limited budgets, making it challenging to hire an in-house IT team with the expertise required to manage complex IT systems. Managed IT Services provide a cost-effective alternative. By outsourcing IT management, small businesses can access a team of experts without the expense of hiring full-time staff. This means you can allocate your resources more efficiently and focus on your core business operations.
Enhanced Security:
Cybersecurity threats are a significant concern for businesses of all sizes. Small businesses, in particular, can be vulnerable to cyberattacks due to limited resources for robust security measures. Managed IT Services include robust cybersecurity solutions, such as firewalls, antivirus software, intrusion detection systems, and regular security audits. These services help protect your business against data breaches, ransomware attacks, and keep your sensitive information safe.
Proactive Monitoring and Maintenance:
Managed IT Service providers offer proactive monitoring of your IT infrastructure. They can identify and address potential issues before they escalate into major problems. This proactive approach helps minimize downtime and ensures that your systems run smoothly, increasing productivity and customer satisfaction. With 24/7 monitoring, your IT provider can respond promptly to any emerging issues, reducing the risk of prolonged outages.
Scalability:
Small businesses often experience fluctuations in their IT needs. Managed IT Services are scalable, allowing you to easily adapt to changes in your business. Whether you're expanding, downsizing, or introducing new technology, your MSP can adjust its services accordingly. This flexibility ensures that you're not overpaying for resources you don't need or struggling to keep up with sudden growth. Scalability allows your IT infrastructure to grow seamlessly with your business.
Focus on Core Competencies:
Outsourcing IT management allows small business owners and employees to concentrate on what they do best – running the business. With IT concerns in capable hands, you can channel your energy into strategic planning, customer service, and business growth. Your staff can focus on their primary roles without the distraction of IT issues, leading to increased productivity and job satisfaction.
Access to Advanced Technology:
Staying up-to-date with the latest technology can be expensive and time-consuming. Managed IT Services provide small businesses with access to cutting-edge technology and software without the hefty upfront costs. This ensures that your business remains competitive and can take advantage of technological advancements such as cloud computing, artificial intelligence, and automation. Your IT provider can also advise you on the best technologies to adopt for your specific needs.
24/7 Support:
IT issues don't adhere to a 9-to-5 schedule. Managed IT Service providers offer round-the-clock support, ensuring that your systems are always available when you need them. This level of support minimizes downtime and reduces the impact of IT-related disruptions on your business operations. Whether it's a critical issue at midnight or a minor glitch during the workday, your IT provider is there to resolve it promptly, keeping your business running smoothly.
Disaster Recovery and Data Backup:
Data loss can be catastrophic for a small business. Managed IT Services include robust data backup and disaster recovery solutions. Your IT provider will implement regular data backups, both onsite and offsite, ensuring that your critical business data is secure and can be quickly restored in case of hardware failure, human error, or cyberattacks. This level of preparedness minimizes downtime, protects your reputation, and prevents significant financial losses.
Compliance and Regulation Adherence:
Certain industries have strict regulations regarding data security and privacy. Managed IT Services providers are well-versed in compliance requirements, such as HIPAA for healthcare or GDPR for data protection. They can help your small business adhere to industry-specific regulations by implementing the necessary security measures, conducting regular audits, and ensuring that your IT infrastructure aligns with compliance standards. This reduces the risk of non-compliance penalties and reputational damage.
Improved Business Continuity:
Managed IT Services play a crucial role in ensuring business continuity. By minimizing IT-related disruptions, your business can operate smoothly even in the face of unforeseen challenges. This resilience is essential for maintaining customer trust and business growth. With reliable IT infrastructure and disaster recovery plans in place, you can confidently navigate unexpected events, whether they are natural disasters, hardware failures, or cybersecurity incidents.
Choosing the Right Managed IT Service Provider
Evaluating Your Business Needs:
Before partnering with a Managed IT Service provider, it's crucial to evaluate your specific business needs thoroughly. Consider factors such as the size of your business, your industry, your current IT infrastructure, and your growth projections. Understanding your unique requirements is the first step in selecting the right IT provider.
Researching and Selecting the Right MSP:
Not all Managed IT Service providers are created equal. Take the time to research and select a provider with a proven track record, industry expertise, and a commitment to meeting your unique requirements. Seek referrals, read customer reviews, and ask potential providers about their experience in serving businesses similar to yours.
Cost Considerations:
While cost savings are a significant benefit of Managed IT Services, it's essential to understand the pricing structure of potential providers fully. Compare pricing models and ensure that you receive a transparent breakdown of costs. Understand what is included in the service agreement and any additional fees that may apply.
Service Level Agreements (SLAs):
Review the Service Level Agreements (SLAs) offered by Managed IT Service Providers. SLAs outline the level of service you can expect, including response times, uptime guarantees, and problem-resolution procedures. A clear SLA helps set expectations and ensures that you receive the support and service quality you require.
Implementing Managed IT Services
Onboarding and Integration:
Once you've selected a Managed IT Service provider, the onboarding process begins. Your provider will work with your team to integrate their services seamlessly into your existing IT infrastructure. This process involves assessing your current setup, identifying areas for improvement, and implementing the necessary changes. Effective onboarding ensures a smooth transition to Managed IT Services without disruptions.
Training and Education:
Ensure that your employees receive adequate training and education on the use of Managed IT Services. This step is essential for maximizing the benefits and efficiency of the services provided. Training sessions can cover topics such as using new software tools, following cybersecurity best practices, and understanding how to access IT support when needed.
Monitoring and Performance:
Ongoing monitoring and performance assessments are essential to ensure that Managed IT Services continue to meet your business needs. Regular reviews with your provider can help identify areas for improvement and optimization. Monitoring tools and reports allow you to track the performance of your IT infrastructure, ensuring that it operates at peak efficiency.
Adapting to Changing Business Needs:
As your business evolves, your IT requirements may change. Work closely with your Managed IT Service provider to adapt and scale services as needed to support your growth and evolving technology needs. Your provider should be a strategic partner who can advise you on technology investments and solutions that align with your business goals.
Unleash the Power of Managed IT Services for Small Business Success
In conclusion, Managed IT Services offer small businesses a wide range of benefits, from cost savings and enhanced security to scalability and access to advanced technology. By outsourcing IT management to a specialized provider, small businesses can focus on their core competencies, improve productivity, and ensure the continuity of their operations.
If you're a small business owner looking to harness the advantages of Managed IT Services, consider partnering with Unique Computing Solutions. Our team of experts is dedicated to providing secure, scalable, and reliable network support tailored to your specific needs.
Contact us today to learn more about how Unique Computing Solutions can help your small business thrive in the digital age.
Network Support vs. Network Security: Striking the Right Balance
In today's digital landscape, businesses heavily rely on their computer networks for seamless operations. These networks not only facilitate communication but also store critical data. Hence, ensuring their uninterrupted performance and security is paramount. This blog delves into the delicate equilibrium between network support and network security and why striking the right balance is essential.
The Role of Network Support
Keeping the Network Operational
Before exploring the balance, let's understand what network support entails. Network support is a comprehensive range of services aimed at ensuring the smooth and uninterrupted functioning of your business's computer network infrastructure. It involves proactive monitoring, troubleshooting, maintenance, and security measures.
- Ensuring Business Continuity: One of the primary goals of network support is to ensure business continuity. Downtime can bring productivity to a standstill and cost your business dearly. Timely support helps prevent such costly interruptions.
- Optimizing Network Performance: Network support is not just about fixing problems; it's also about optimizing network performance. Professionals ensure your network operates at peak efficiency, enhancing both employee productivity and customer satisfaction.
Cost Savings Through Preventive Measures
While network support might seem like an added expense, it can lead to significant cost savings in the long run.
- Preventing Costly Network Failures: By proactively addressing network issues, support services prevent costly network failures that can result in downtime, data loss, and reputational damage.
- Safeguarding Data: Robust data backup and recovery strategies are part of network support. This safeguards essential information, ensuring business continuity and regulatory compliance.
- Scalability and Growth: Effective network support is scalable. As your business grows, your network should be able to accommodate the increased load. Support services help plan and implement necessary expansions without compromising performance.
The Importance of Network Security
Protecting Against Cyber Threats
In an era of constant cyber threats, network security is paramount. Cybercriminals are becoming increasingly sophisticated, making it crucial to have robust security measures in place.
- Safeguarding Customer Trust: A security breach can erode customer trust and result in financial losses and legal liabilities. Network security measures protect your data from breaches, ransomware, and other malicious attacks, maintaining customer trust.
- Meeting Regulatory Requirements: many industries have strict regulations regarding data security and privacy. Network security experts stay updated on these regulations and implement necessary measures to keep your business compliant.
Ensuring Confidentiality
Network security ensures the confidentiality of sensitive data. Whether it's proprietary business information or customer data, network security measures prevent unauthorized access and data leaks.
- Authentication and Authorization: Proper authentication and authorization protocols are essential components of network security. They ensure that only authorized personnel can access sensitive information.
- Encryption: Encryption is a vital tool in network security. It converts data into a coded format that can only be deciphered with the correct decryption key, protecting data during transmission and storage.
The Cost of Ignoring Network Security
Financial Repercussions
While we've discussed the cost savings associated with network support, it's equally crucial to understand the potential financial repercussions of neglecting network security.
- Loss of Revenue: A security breach or data leak can lead to lost revenue, not to mention the cost of resolving the breach and potential legal consequences.
- Reputational Damage: Customers and clients rely on your business to be secure. A security breach can damage your reputation, resulting in lost business and customer trust.
Legal Consequences
Neglecting network security can lead to legal consequences, including fines and penalties for failing to meet regulatory requirements.
Remediation Costs
In the aftermath of a security breach, your business will incur remediation costs, including investigating the breach, notifying affected parties, and implementing security improvements.
Striking the Balance
Collaboration between Network Support and Security
Balancing network support and security is not an either-or-scenario but a collaboration. Here's how you can strike the right balance:
- Regular Assessments: Regular assessments of your network's performance and security vulnerabilities can help identify areas that need attention from both support and security perspectives.
- Communication: Effective communication between network support and security teams is essential. They must work together to implement strategies that prioritize both performance and security.
- Customized Solutions: Consider customized solutions that address your specific business needs. Not all businesses require the same level of support and security, so tailor your approach accordingly.
- Training and Awareness: Invest in training and awareness programs for your employees. Human error is a common cause of security breaches, and educating your workforce can reduce the risk.
Unique Computing Solutions: Your Balanced Approach Partner
At Unique Computing Solutions (UCS), we understand the delicate balance required between network support and network security. Our experienced team is well-versed in providing comprehensive solutions that prioritize both performance and security.
Expertise
Our team of network support professionals and security experts have years of experience in network management and cybersecurity. We have the knowledge and skills to provide you with a balanced approach that ensures the safety and efficiency of your network.
Cutting-Edge Technology
UCS leverages cutting-edge technology and tools to provide you with the best network support and security solutions. Our state-of-the-art monitoring systems and security measures ensure that your network is always in safe hands.
Customized Solutions
We understand that every business is unique. That's why we offer customized solutions tailored to your specific needs. Whether you're a small business or a large enterprise, we have the expertise to provide you with the right level of support and security.
Proactive Monitoring and Rapid Response
UCS's proactive monitoring approach means we often resolve problems before they impact your operation. In the event of an issue, our rapid response team is just a call away, ensuring your network stays up and running.
Securing Your Business's Digital Future
In conclusion, the balance between network support and network security is not a choice but a necessity for businesses of all sizes. striking the right equilibrium safeguards your network, enhances performance, and ultimately saves you time and money.
To experience the benefits of a balanced approach, look no further than Unique Computing Solutions. With UCS as your partner, you can focus on what you do best - growing your business and serving your customers - knowing that your network is in expert hands.
Are you ready to secure your network and boost your business's success? Contact Unique Computing Solutions today for personalized solutions that will keep your operations running smoothly and securely.
How Can Managed IT Services Help in Scaling My Business?
Businesses are constantly evolving, and technology plays a crucial role in their growth and success. Managing IT infrastructure can be a daunting task, especially for small and medium-sized enterprises (SMEs) striving to scale their operations. This is where Managed IT Services come into play. In this comprehensive blog, we will explore how Managed IT Services can benefit your business and help it scale to new heights.
What Are Managed IT Services?
Managed IT services encompass a range of IT solutions and support provided by third-party experts, often referred to as managed service providers (MSPs). These services are crafted to lift the weight of IT management from your shoulders, enabling you to concentrate on your core business activities.
Key Services Offered by Managed IT Service Providers:
Managed IT services typically include:
- Proactive IT Support: MSPs monitor your IT infrastructure 24/7, proactively identifying and resolving issues before they impact your business operations.
- Cybersecurity Solutions: Comprehensive security measures, such as firewall protection, antivirus software, and data encryption, are put in place to safeguard your business data from cyber threats.
- Data Backup and Recovery: Regular data backups ensure that your critical business data is secure and recoverable in the event of a disaster.
- Network Management: Managed IT Service Providers optimize your network for efficiency and reliability, ensuring minimal downtime.
- Cloud Services: They offer cloud-based solutions, allowing your business to leverage the scalability and flexibility of cloud computing.
The Role of Managed IT Services in Business Scaling
Now that we have a clear understanding of what Managed IT Services entail, let's delve into how they can facilitate the growth and scaling of your business.
Cost-Efficiency:
One of the primary advantages of Managed IT Services is cost efficiency. Instead of hiring and maintaining an in-house IT team, which can be expensive and challenging to manage, you can outsource your IT needs to a specialized MSP. This reduces labor costs, eliminates the need for expensive IT infrastructure, and allows you to pay for only the services you require.
Managed IT Services operate on a subscription-based model, which means you can budget your IT expenses more predictably. This cost predictability is especially beneficial for SMEs, as it enables you to allocate resources more efficiently and redirect funds to other critical areas of your business, such as marketing, product development, or expanding your customer base.
Additionally, MSPs often have established relationships with technology vendors, allowing them to access hardware and software at reduced costs, which they can then pass on to their clients. This means you can benefit from cutting-edge technology without breaking the bank.
Enhanced Productivity:
With Managed IT Services, you can ensure the consistent performance of your IT systems. We minimize downtime caused by technical issues, enabling your employees to concentrate on their core responsibilities instead of troubleshooting IT problems. This boost in productivity can lead to accelerated business growth.
Consider a scenario where your business experiences frequent network disruptions or software crashes. In such cases, not only does productivity suffer, but your employees also become frustrated, leading to decreased morale. Managed IT Services providers proactively monitor your systems, often detecting and addressing potential issues before they impact your operations. This translates to improved employee satisfaction, higher work output, and ultimately, business growth.
Moreover, the availability of IT support around the clock ensures that you can handle tasks and transactions across different time zones without worrying about system glitches or downtime.
Scalability:
As your business expands, your IT needs will evolve. Managed IT Service Providers offer scalable solutions that can adapt to your changing requirements. Whether you need to add more users, expand your server capacity, or integrate new software, MSPs can quickly accommodate your growth without major disruptions.
Scalability extends beyond just adding more hardware or software licenses. It involves a strategic approach to IT planning, aligning your technology resources with your business goals. For example, if you plan to enter new markets or launch additional product lines, your MSP can design an IT infrastructure that supports these objectives.
Moreover, Managed IT Service Providers can help you leverage cloud computing solutions, which offer unparalleled scalability. Cloud services allow you to scale up or down based on demand, paying only for the resources you use. This flexibility is essential for businesses experiencing seasonal fluctuations or rapid growth spurts.
Robust Security:
In an era where cyber threats are constantly evolving, maintaining robust cybersecurity is crucial for any business. Managed IT Service Providers are well-equipped to implement and manage security measures that protect your sensitive data and systems from cyberattacks.
Cybersecurity breaches can have devastating consequences, including data loss, reputational damage, and legal liabilities. MSPs stay up-to-date with the latest security threats and best practices to keep your business protected. They implement multi-layered security solutions, including firewalls, intrusion detection systems, antivirus software, and employee training programs.
Additionally, they can perform regular security audits and vulnerability assessments to identify and address potential weaknesses in your IT infrastructure. By proactively managing your cybersecurity, MSPs reduce the risk of security breaches and help you maintain customer trust, which is essential for scaling your business.
Strategic Planning:
Managed IT Service Providers don't just offer technical support; they also provide strategic IT planning. They can assess your current infrastructure, identify areas for improvement, and recommend solutions that align with your business objectives. This proactive approach ensures that your IT systems are always optimized for growth.
Strategic planning involves analyzing your business's long-term goals and aligning your technology roadmap accordingly. For example, if your expansion strategy involves opening new branches or entering new markets, your MSP can develop a plan that includes network expansion, hardware procurement, and software integration to support these initiatives.
Moreover, Managed IT Service Providers can help you adopt emerging technologies that give you a competitive edge. Whether it's implementing artificial intelligence, machine learning, or automation, they can guide you through the adoption process and ensure that these technologies are seamlessly integrated into your business operations.
Choosing the Right Managed IT Service Provider
Selecting the right Managed IT Service Provider is crucial to realizing the full potential of these services for your business. Here are some key factors to consider when making your choice:
- Experience and Expertise: Look for an MSP with a proven track record and extensive experience in providing IT services to businesses in your industry. A provider with relevant expertise is more likely to understand your unique challenges and requirements.
- Service Level Agreements: Review the SLAs offered by potential MSPs carefully. Ensure that they align with your business goals and guarantee prompt response times and issue resolution.
- Scalability: Choose an MSP that can accommodate your business's growth. They should have the flexibility to adapt to your changing IT requirements without causing disruptions.
- Security Measures: Verify the security measures in place to protect your data and systems. A robust cybersecurity framework is non-negotiable in today's digital landscape.
- References and Testimonials: Don't hesitate to ask for references or read testimonials from existing clients. This will give you insight into the MSP's reputation and customer satisfaction levels.
Unleashing Your Business's Full Potential with Managed IT Services
Managed IT services offer a strategic advantage to businesses looking to scale their operations while maintaining efficiency and security. They provide cost-effective solutions, enhance productivity, and ensure that your IT infrastructure evolves seamlessly with your business growth. Choosing the right managed IT service provider lets you leverage their expertise while focusing on growing your business.
Ready to experience the benefits of managed IT services firsthand? Contact Unique Computing Solutions today to discuss how our tailored solutions can help your business scale successfully.
What Are the Latest IT Solutions for Secure, Efficient Operations?
In the dynamic world of business, where competition is fierce and technology evolves at lightning speed, staying abreast of the latest IT solutions is not just beneficial – indeed, it’s imperative. These solutions are the bedrock of secure, efficient operations and can significantly impact a company’s growth, sustainability, and resilience. In this comprehensive guide, we’ll explore the latest IT solutions that are essential for businesses aiming to thrive in today’s digital landscape.
The Critical Role of IT Solutions in Modern Business
IT solutions are more than just technological tools; they are the lifeline of modern businesses. They streamline operations, protect critical data, facilitate communication, and drive innovation. In a world where data breaches and operational inefficiencies can lead to significant losses, investing in the right IT solutions is paramount.
 Pioneering IT Solutions for Modern Business
Pioneering IT Solutions for Modern Business
- Advanced Cloud Computing Services: Cloud computing has evolved beyond basic storage solutions. Today, it offers advanced services like Platform-as-a-Service (PaaS) and Infrastructure-as-a-Service (IaaS), providing businesses with scalable, flexible, and cost-effective IT infrastructure.
- Comprehensive Cybersecurity Measures: The sophistication of cyber threats demands equally sophisticated cybersecurity measures. Next-generation firewalls, endpoint protection, and AI-driven security analytics are becoming indispensable for safeguarding business data and infrastructure.
- Internet of Things (IoT) Integration: IoT is not just about connecting devices; it’s about harnessing data from those connections to optimize operations. IoT solutions can lead to significant improvements in areas like supply chain management, predictive maintenance, and energy management.
- AI and Machine Learning Innovations: AI and ML are no longer futuristic concepts. They are here, revolutionizing everything from customer service with chatbots to process automation and predictive analytics. These technologies are key to gaining a competitive edge.
- Blockchain Beyond Cryptocurrency: Blockchain is proving its worth beyond the realm of digital currencies. Its applications in ensuring data integrity, supply chain transparency, and secure transactions are invaluable for various industries.
Enhancing Business Operations with Cutting-Edge IT
- Unified Communications as a Service (UCaaS): UCaaS represents the next level in communication solutions, integrating voice, video, messaging, and collaboration tools into a seamless, cloud-based service. This fosters better teamwork and productivity, especially in remote work environments.
- Data Analysis and Business Intelligence Tools: In the age of big data, data analytics and business intelligence tools are crucial. They provide actionable insights, help in understanding market trends, and aid in making informed strategic decisions.
- Edge Computing for Real-time Processing: Edge computing addresses the limitations of cloud computing by processing data closer to where it’s generated. This is particularly beneficial for applications requiring low latency and real-time analysis.
- VR and AR for Enhanced Experiences: Virtual and Augmented Reality technologies are not just for gaming. They are transforming training, product demonstration, and customer engagement in industries like healthcare, real estate, and retail.
- Embracing Green IT: Sustainable IT practices are becoming a priority, Green IT focuses on reducing the environmental impact of technology through energy-efficient hardware, eco-friendly practices, and sustainable data center operations.
Streamlining and Securing Business with IT Innovations
- Mobile Workforce Solutions: The rise of remote work has made mobile workforce solutions essential. These solutions include secure mobile device management, virtual private networks (VPNs), and collaboration tools that enable employees to work effectively from anywhere.
- Disaster Recovery and Business Continuity: Disaster recovery and business continuity planning are critical for minimizing the impact of unexpected events. Cloud-based backup solutions, redundant systems, and well-documented recovery plans ensure businesses can quickly resume operations after a disruption.
- Compliance and Regulatory Solutions: As regulations become more stringent, businesses need compliance and regulatory solutions to navigate the complex legal landscape. These solutions help in data protection, privacy compliance, and adherence to industry-specific regulations.
- Custom Software Development: Sometimes off-the-shelf solutions don’t meet specific business needs. Custom software development allows businesses to have tailored applications that perfectly fit their operational requirements.
Optimizing IT Infrastructure for Future-Ready Businesses
- IT Consulting and Strategy: IT consulting and strategy services are invaluable for businesses looking to align their technology with their strategic goals. Expert consultants can provide insights, assess technology needs, and help in planning for future growth.
- Network Infrastructure and Management: Robust network infrastructure and management are crucial for seamless operations. This includes high-speed networking, reliable connectivity, and network security measures to ensure data integrity and accessibility.
- Cloud Migration and Management: Cloud migration and management services help businesses transition to cloud environments smoothly. This includes selecting the right cloud platform, migrating data and applications, and managing cloud resources effectively.
- Server Virtualization: Server virtualization allows businesses to run multiple virtual servers on a single physical server, optimizing resource utilization and reducing hardware costs. It also enhances flexibility and scalability.
- Remote Monitoring and Management (RMM): RMM solutions enable proactive monitoring of IT infrastructure. This helps in identifying and resolving issues before they escalate, ensuring minimal downtime and optimal performance.
- Voice Over Internet Protocol (VolP) Solutions: VolP solutions offer cost-effective, flexible communication options. They provide features like call forwarding, voicemail, and conferencing, making communication seamless and efficient.
Fostering a Culture of Innovation Through IT
In today’s fast-paced business environment, fostering a culture of innovation is not just a luxury; it’s a necessity for survival and growth. Information Technology (IT) plays a pivotal role in cultivating this culture. It’s the engine that powers innovation, drives change, and opens new frontiers for businesses to explore. Here’s how IT is instrumental in fostering a culture of innovation.
Empowering Creativity with Tools and Platforms:
IT provides the tools and platforms that empower employees to bring their creative ideas to life. From collaborative software to advanced design tools, technology equips the workforce with everything they need to innovate. For instance, cloud-based platforms enable teams to collaborate in real time, regardless of their physical location, sparking creativity and facilitating the exchange of ideas.
Democratizing Access to Information:
Access to information is crucial for innovation. IT solutions democratize this access, ensuring that every team member can tap into the data and insights they need. Whether it’s through internal knowledge bases, data analytics tools, or online research databases, IT ensures that the fuel for innovation – information – is readily available.
Streamlining Processes for Efficiency:
Innovation isn’t just about new products or services; it’s also about finding better ways to do things. IT streamlines business processes, automates repetitive tasks, and eliminates inefficiencies. This not only saves time and resources but also frees up employees to focus on creative and innovative endeavors.
Implementing the Right IT Solutions with Unique Computing Solutions
Navigating the vast landscape of IT solutions can be overwhelming. That’s where Unique Computing Solutions comes into the picture. We specialize in identifying and implementing the right IT solutions tailored to your specific business needs.
Tailored IT Strategies for Your Business:
Every business has unique challenges and goals. Recognizing this, Unique Computing Solutions offers customized IT strategies that specifically align with your business objectives. As a result, this ensures that you leverage the right technologies for maximum impact.
Expert Implementation and Support:
Implementing new IT solutions can be complex. Our team of experts ensures a smooth transition, minimizing disruptions to your operations. We also provide ongoing support and maintenance, ensuring your IT infrastructure remains robust and up-to-date.
Proactive IT Management:
We firmly believe in proactive IT management. Consequently, by consistently anticipating potential issues and diligently staying ahead of technological trends, we actively help you avoid downtime. Furthermore, this approach ensures your business keeps running smoothly, thereby maintaining operational continuity and efficiency.
Secure and Efficient Operations with Unique Computing Solutions
The right IT solutions are pivotal for secure, efficient operations in today’s digital landscape. From advanced cloud services to AI and green IT, these technologies are reshaping the way businesses operate. However, understanding and implementing them can be challenging.
Unique Computing Solutions is your partner in this journey. With our expertise, customized strategies, and ongoing support, we help you navigate the complexities of modern IT solutions. We ensure that your business is not just keeping up but staying ahead in the technological race.
Are you ready to transform your business with the latest IT solutions? If so, don’t hesitate to contact Unique Computing Solutions today. Let us empower your business with secure, efficient, and innovative IT solutions, meticulously tailored to your unique needs. Together, we can seamlessly unlock new opportunities and collaboratively drive your business towards a successful future.
Why is Network Support Vital for Your Business?
In today’s digital age, businesses rely heavily on their computer networks to operate efficiently. Whether you run a small startup or a large corporation, your network is the backbone of your daily operations. Any disruption or downtime can lead to lost productivity, revenue, and ultimately, customer trust. This is where professional network support comes into play.
Network Support: What Is It?
Before delving into the reasons why network support is vital for your business, let’s first understand what network support is:
Network support refers to the comprehensive range of services and solutions aimed at ensuring the smooth and uninterrupted functioning of a business’s computer network infrastructure. It involves proactive monitoring, troubleshooting, maintenance, and security measures to keep your network up and running.
The Importance of Network Support
- Enhancing Security: In an era of constant cyber threats, network security is paramount. Network support experts employ the latest security measures to protect your data from breaches, ransomware, and other malicious attacks. By safeguarding your network, they help you maintain the trust of your customers and clients.
- Optimizing Performance: Network Support goes beyond fixing problems; it’s about optimizing network performance. Professionals ensure that your network operates at its peak efficiency, providing a seamless experience for both employees and customers. This optimization can lead to increased productivity and customer satisfaction.
- Cost Savings: While it may seem like an added expense, network support can actually save your business money in the long run. By preventing costly network failures and security breaches, you avoid the financial repercussions of downtime, data loss, and reputational damage.
- Compliance and Regulations: Many industries have strict regulations regarding data security and privacy. Network support experts stay up-to-date with these regulations and implement the necessary measures to keep your business compliant. Failure to comply with industry standards can lead to fines and legal consequences.
- Data Backup and Recovery: Data loss can be catastrophic for businesses. Network support includes robust data backup and recovery strategies to ensure that your critical data is safe and can be quickly restored in case of unexpected incidents. This safeguarding of essential information is essential for business continuity and regulatory compliance.
The Cost of Not Having Network Support
While we’ve discussed the cost savings associated with network support, it’s equally important to understand the potential financial repercussions of not having adequate support in place. Failing to invest in network support can lead to several costly consequences:
- Loss of Productivity: Downtime due to network issues can bring your business to a standstill. When employees can’t access critical applications or data, work comes to a halt, resulting in lost productivity and missed deadlines. The longer the downtime, the more revenue you stand to lose.
- Data Loss and Recovery Costs: Without network support’s robust data backup and recovery solutions, data loss can be catastrophic. Recovering lost data can be a time-consuming and expensive process, and in some cases, complete data loss may be irreversible.
- Reputation Damage: Customers and clients rely on your business to be accessible and secure. A network breach or extended downtime can damage your reputation and erode customer trust, leading to lost business and potential legal liabilities.
- Emergency IT Costs: When network issues arise unexpectedly, you may be forced to bring in emergency IT support at a premium cost. These unplanned expenses can significantly impact your budget.
- Missed Business Opportunities: In today’s fast-paced business world, missing out on opportunities can be just as costly as a direct expense. Inability to respond to customer needs or take advantage of market trends due to network issues can lead to missed revenue and growth potential.
Unique Computing Solutions: Your Network Support Partner
Now that you understand the importance of network support, it’s crucial to partner with a reliable and experienced provider. This is where Unique Computing Solutions comes in.
Our Expert Team:
At Unique Computing Solutions, we take pride in our highly skilled and certified team of network support professionals. Our experts have years of experience in network management and cybersecurity, making us the ideal partner for your business.
Advanced Technology:
We leverage cutting-edge technology and tools to provide you with the best network support solutions. Our state-of-the-art monitoring systems and security measures ensure that your network is always in safe hands.
 Client Success Stories:
Client Success Stories:
Don’t just take our word for it; hear what our satisfied clients have to say. Read our success stories to understand how UCS has transformed businesses like yours through reliable network support.
Customized Solutions:
We understand that every business is unique. That’s why we offer customized solutions tailored to your specific needs. Whether you’re a small business or a large enterprise, we have the expertise to provide you with the right level of support.
Proactive Monitoring and Maintenance:
Prevention is key. With UCS, you can rest assured that we’re constantly monitoring your network for potential issues. Our proactive approach means we often resolve problems before they impact your operations.
Rapid Response:
In the event of an issue, our rapid response team is just a call away. We’re committed to minimizing downtime and ensuring your network stays up and running.
Securing Your Business’s Digital Future
In summary, network support is not a luxury but a necessity of all sizes. It safeguards your network, enhances performance, and ultimately saves you time and money. To experience the benefits of professional, look no further than Unique Computing Solutions.
With Unique Computing Solutions as your network support partner, you can focus on what you do best – growing your business and serving your customers – knowing that your network is in expert hands.
Ready to secure your network and boost your business’s success? Well, contact Unique Computing Solutions today for a personalized solution that will keep your operations running smoothly and securely.










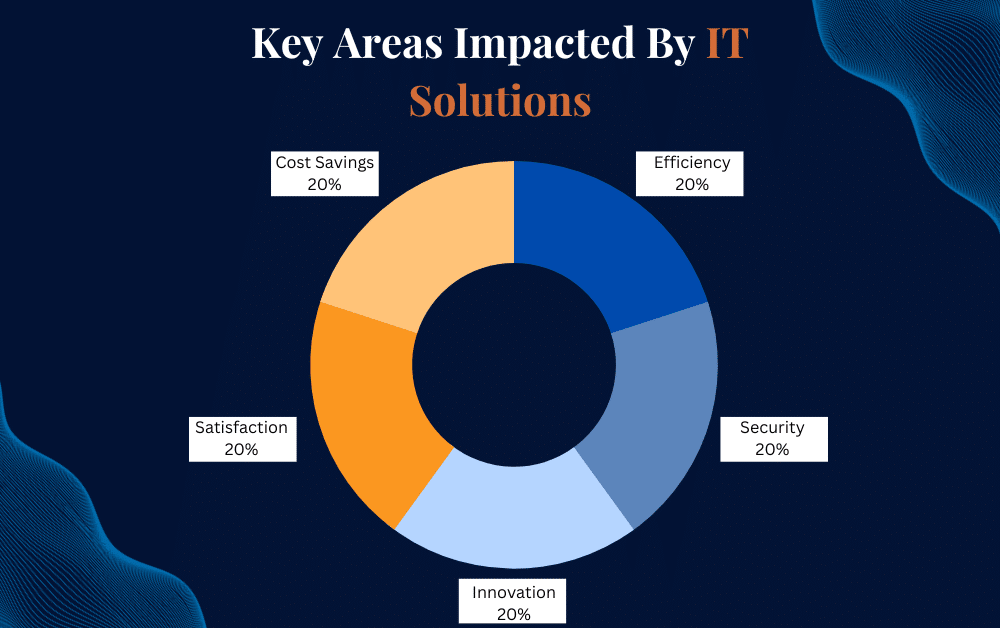 Pioneering IT Solutions for Modern Business
Pioneering IT Solutions for Modern Business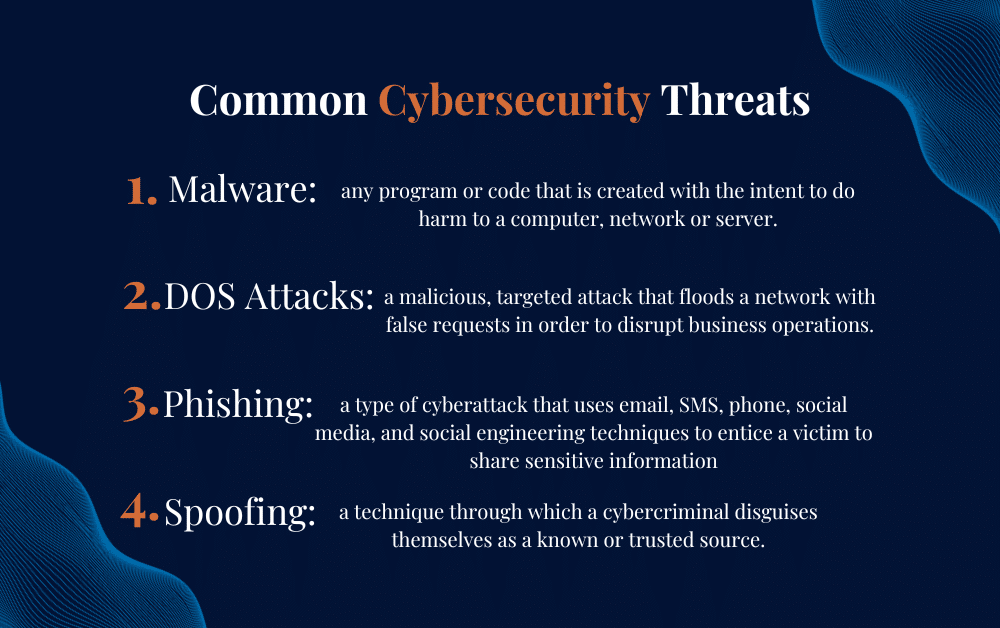
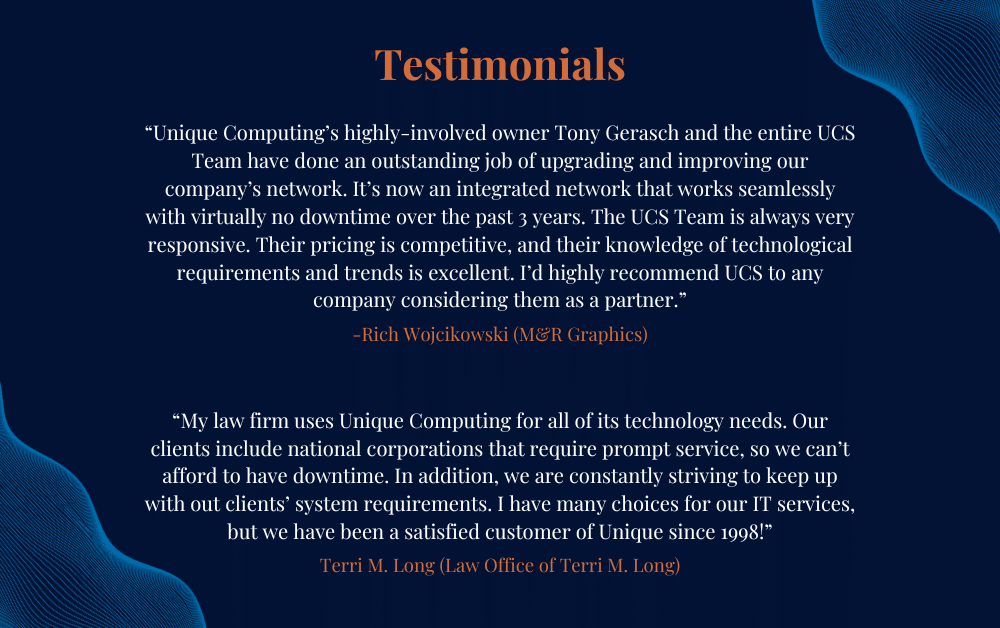 Client Success Stories:
Client Success Stories: